If you use a Mac, it could be at risk of two new threats. While Apple has a reputation for having ironclad security, these two pieces of malware are designed to trick you and steal your data.
Jamf Threat Labs, an organization that focuses on the safety of Apple products, says the malware threats are part of a year-long attack on Mac systems.
The group says hackers are using them to harvest data. Attacks like these are constantly happening, according to the lab. That makes it all the more important for those who use a Mac to ensure your data is locked down.
It’s important to note that, according to the lab, these hackers largely target the crypto industry, putting those individuals, particularly, at risk. That said, all Mac users should still exercise caution.
MacBook Pro (Kurt “CyberGuy” Knutsson)
Malware posing as ads
Before we get into the malware, let’s talk about Arc Browser. For those unfamiliar with it, Arc Browser is a Mac web browser that looks to give users a unique experience. First and foremost, the main focus is on the webpage. Any buttons you might find in a traditional browser are relegated to a sidebar. It uses a bookmark system that gives you multiple workspaces. It also has automated tab management.
In other words, many Mac users would consider Arc Browser an upgrade over the already-included Safari. And its ever-growing popularity makes it a huge target for hackers.
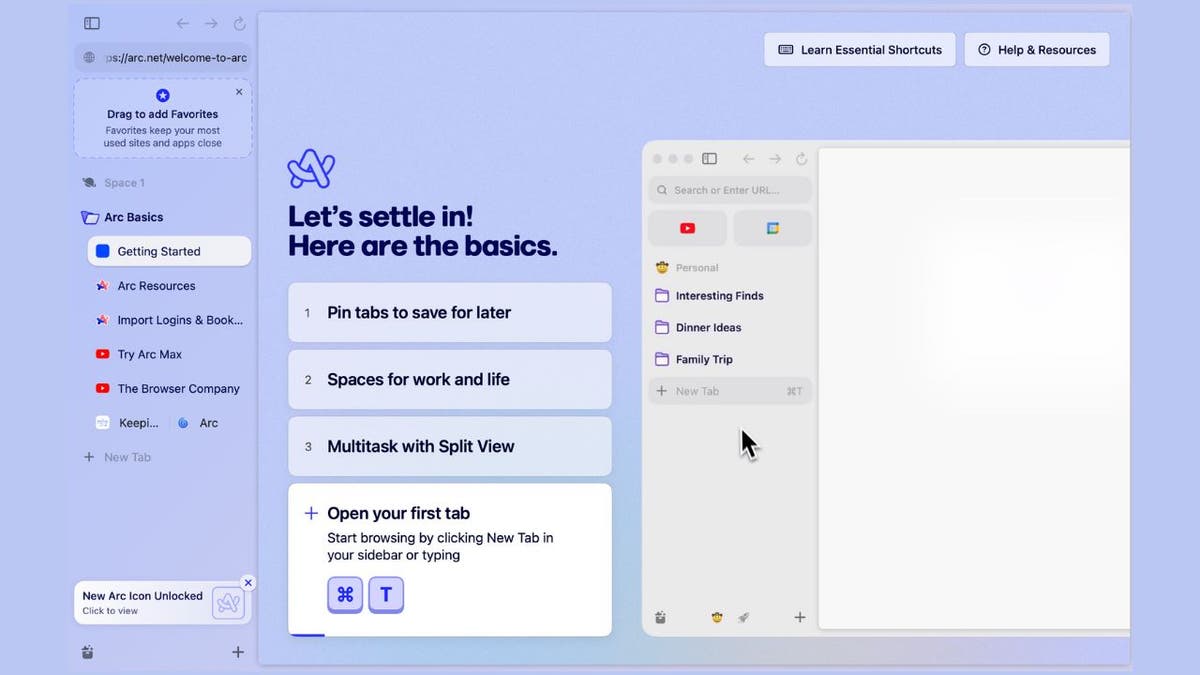
Legitimate Arc Browser website (Kurt “CyberGuy” Knutsson)
MORE: HOW CRYPTO IMPOSTERS ARE USING CALENDY TO INFECT MACS WITH MALWARE
How fake Arc Web Browser ads conceal dangerous malware
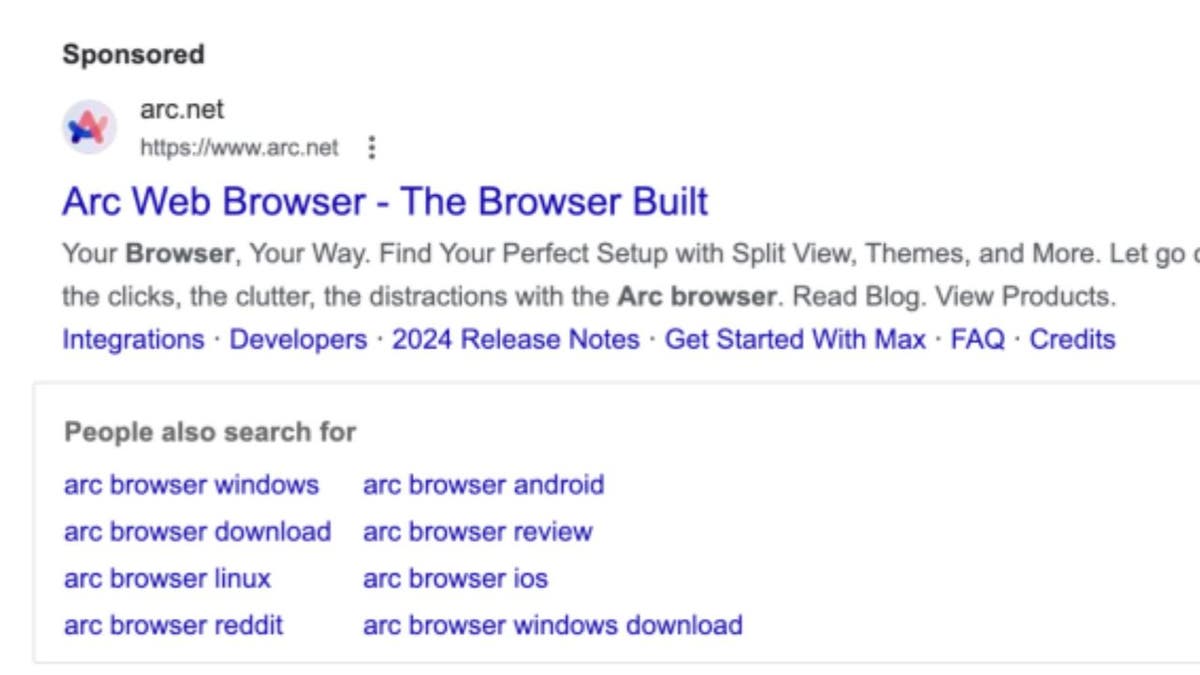
In this attack, hackers are hiding malware in advertisements posing as ads for Arc Browser, as seen below.
Malicious site aricl[.]net that imitates the legitimate arc.net (Jamf Threat Labs)
The ad redirects to a malicious lookalike site: arc.net vs. aricl.net
Instead of taking you to the legitimate download page for the Arc web browser, the ad takes you to a lookalike malicious site, aricl[.]net, that imitates the legitimate arc.net and hosts malware.
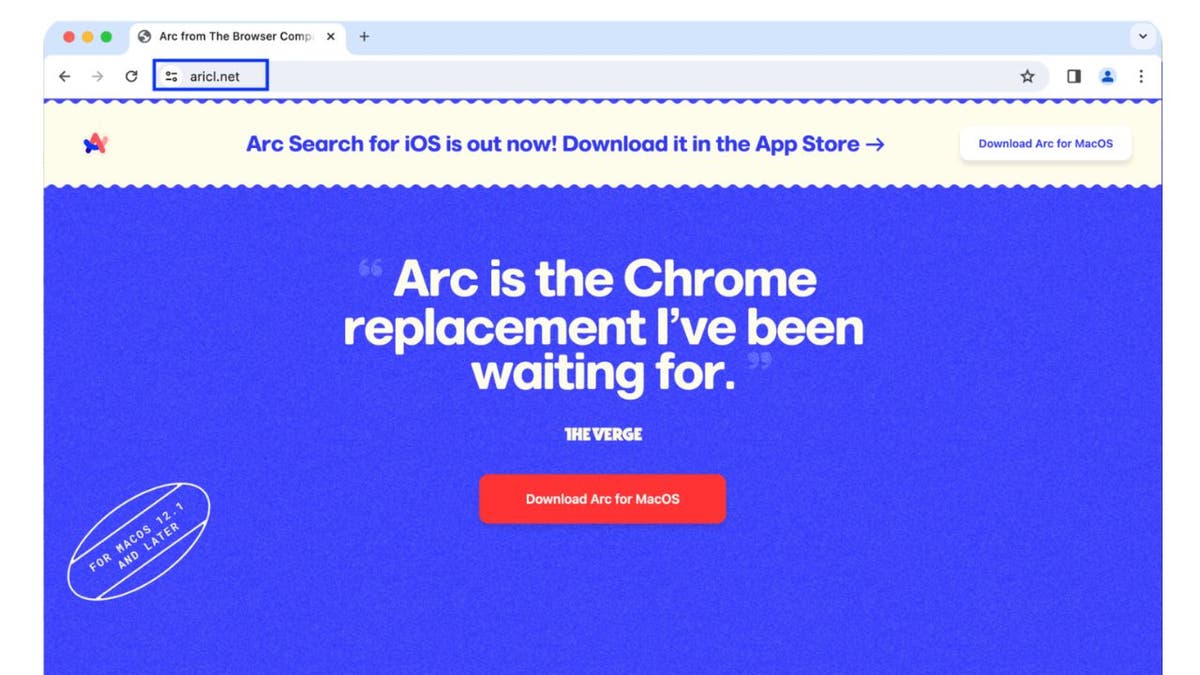
Image of the malicious aricl[.]net site (Jamf Threat Labs)
Malware disguised as Arc Browser unleashes Atomic Stealer
Once you download malware posing as Arc Browser, the malware unleashes an Atomic stealer. It’s a fake prompt that looks like a normal System Preferences prompt asking you for your password. Once the hackers
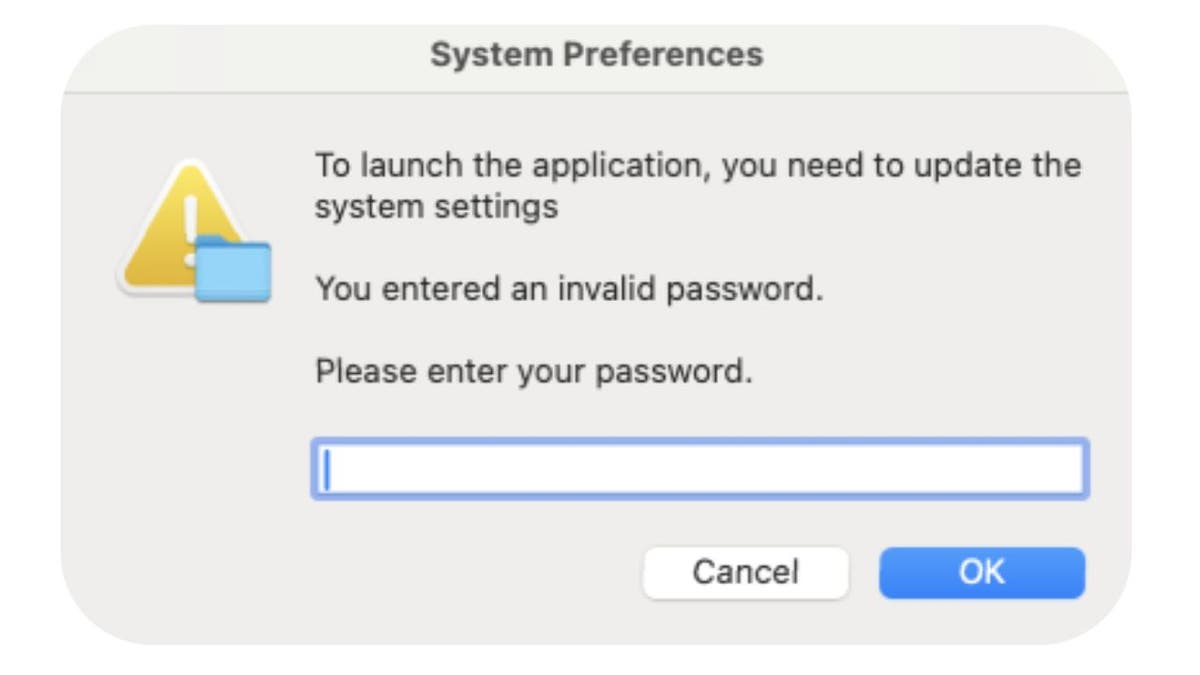
Fake system preferences prompt (Jamf Threat Labs)
Even worse, these so-called “ads” can appear as sponsored advertisements in a Google search. Jamf Threat Labs says these links can only be accessed through a generated sponsored link and not accessed directly. Attempts to access the malicious website directly returned an error message. This is presumably done to evade detection.
Fake meeting software
The researchers at Jamf Threat Labs have also discovered a fake website that offers malware hidden as free group meeting scheduling software. Meethub[.]gg appears to be legitimate. The company posts articles on Medium and has more than 8,000 followers on X, at the time of publishing. It, however, hosts malware that’s related to Realst, another piece of malware designed to drain crypto wallets.
Some of the attacks involving Meethub use social engineering. A hacker might approach their victim looking to interview them for a job or a podcast. In order to meet, they ask the victim to download Meethub’s software. According to Jamf, these attacks can sometimes lead to big paydays for hackers.
Meethub website (Jamf Threat Labs)
How to protect yourself
1. Don’t download bootleg software: It’s not worth the risk to download bootleg software. It exposes your device to potential security threats like viruses and spyware. If someone emails you a link for a download, make sure it’s from a reputable source and scan it.
2. Don’t click on suspicious links or files: If you encounter a link that looks suspicious, misspelled or unfamiliar, avoid clicking on it. Instead, consider going directly to the company’s website by manually typing in the web address or searching for it in a trusted search engine. Most often, the first or second result that comes up is legitimate. If you see the word “Sponsored “above the search result, take a beat before clicking it and consider clicking on the result below it.
3. Have good antivirus software: The best way to protect yourself from clicking malicious links that install malware that may get access to your private information is to have antivirus protection installed on all your devices. This can also alert you of any phishing emails or ransomware scams. Get my picks for the best 2024 antivirus protection winners for your Mac, Windows, Android & iOS devices.
MORE: STEALTHY BACKDOOR MAC MALWARE THAT CAN WIPE OUT YOUR FILES
What to do if you’ve been hacked
If it has already happened, and you’ve been hacked, then you should take immediate action to minimize the damage and secure your device. Here are some steps that you can follow:
Change your passwords
If hackers have recorded your passwords, they could access your online accounts and steal your data or money. On another device (i.e., your laptop or desktop), you should change your passwords for all your important accounts, such as email, banking, social media, etc. You want to do this on another device so the hacker isn’t recording you setting up your new password on your hacked device. And you should also use strong and unique passwords that are hard to guess or crack. You can also use a password manager to generate and store your passwords securely.
Enable two-factor authentication
You’ll want to activate two-factor authentication for an extra layer of security.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
Monitor your accounts and transactions
You should check your online accounts and transactions regularly for any suspicious or unauthorized activity. If you notice anything unusual, report it to the service provider or authorities immediately. You should also review your credit reports and scores to see if there are any signs of identity theft or fraud.
Use identity theft protection
Identity theft protection companies can monitor personal information like your home title, Social Security number, phone number and email address and alert you if it is being used to open an account. They can also assist you in freezing your bank and credit card accounts to prevent further unauthorized use by criminals. See my tips and best picks on how to protect yourself from identity theft.
Contact your bank and credit card companies
If hackers have obtained your bank or credit card information, they could use it to make purchases or withdrawals without your consent. You should inform your bank and credit card companies of the situation. They can help you freeze or cancel your cards, dispute any fraudulent charges, and issue new cards for you.
Alert your contacts
If hackers have accessed your email or social media accounts, they could use them to send spam or phishing messages to your contacts. They could also impersonate you and ask for money or personal information. You should alert your contacts and warn them not to open or respond to any messages from you that seem suspicious or unusual.
MORE: HOW A FLEW IN iPHONE’S SECURITY COULD LEAVE YOU LOCKED OUT
Kurt’s key takeaways
While Macs are generally secure devices, that hasn’t stopped hackers from stealing data. In fact, these two new attacks show how creative they can be while trying to break into your device. That’s why it’s so important to have good antivirus software and safety practices.
Good safety practices are even more essential for people who trade and use cryptocurrencies in these particular situations. As mentioned before, these attacks focus largely on draining crypto wallets. And while anyone can be hacked, crypto users have a higher risk. So take the time to assess a link before clicking on it. Don’t just download software because someone tells you to. Do your research. At the end of the day, it will help keep your data and your wallet safe.
CLICK HERE TO GET THE FOX NEWS APP
Are you worried about hackers finding more creative ways to break into your computer? If you use crypto, how are you keeping your crypto wallet safe? Let us know by writing us at Cyberguy.com/Contact
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter
Ask Kurt a question or let us know what stories you’d like us to cover
Answers to the most asked CyberGuy questions:
Copyright 2024 CyberGuy.com. All rights reserved.